docker 第二课
构建nginx镜像
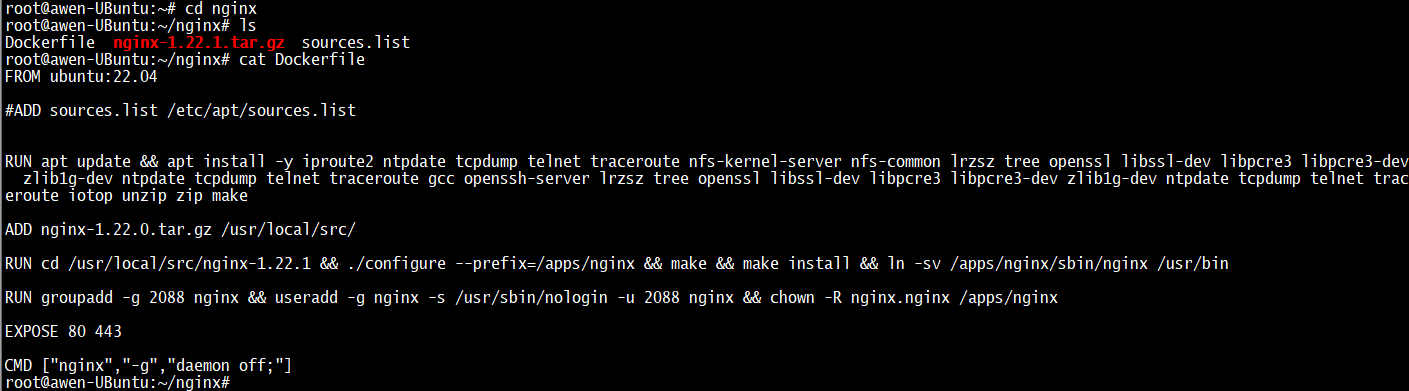
root@awen-UBuntu:~/nginx# cat Dockerfile
FROM ubuntu:22.04
#ADD sources.list /etc/apt/sources.list
RUN apt update && apt install -y iproute2 ntpdate tcpdump telnet traceroute nfs-kernel-server nfs-common lrzsz tree openssl libssl-dev libpcre3 libpcre3-dev zlib1g-dev ntpdate tcpdump telnet traceroute gcc openssh-server lrzsz tree openssl libssl-dev libpcre3 libpcre3-dev zlib1g-dev ntpdate tcpdump telnet traceroute iotop unzip zip make
ADD nginx-1.22.0.tar.gz /usr/local/src/
RUN cd /usr/local/src/nginx-1.22.1 && ./configure --prefix=/apps/nginx && make && make install && ln -sv /apps/nginx/sbin/nginx /usr/bin
RUN groupadd -g 2088 nginx && useradd -g nginx -s /usr/sbin/nologin -u 2088 nginx && chown -R nginx.nginx /apps/nginx
EXPOSE 80 443
CMD ["nginx","-g","daemon off;"]
root@awen-UBuntu:~/nginx# docker run -it -p 80:80 --name nginx nginx:v20221025
基于 docker 实现对容器的 CPU 和内存的资源限制
cgroupfs是文件级别的资源限制控制器 ,现在使用systemd
软限制
root@awen-UBuntu:~# docker run -it -d -m 512m --memory-reservation 511m nginx:1.18.0-alpine
root@awen-UBuntu:~# docker run -it --rm lorel/docker-stress-ng --help
-c N, --cpu N start N workers spinning on sqrt(rand()) 启动N个workers进行cpu的压测
--vm N start N workers spinning on anonymous mmap 启动N个workers进行内存压测
--vm-bytes N allocate N bytes per vm worker (default 256MB) workers内存压测字节数 锁定一定的字节数给每个worker
两个内存worker 每个内存消耗256M
Example: stress-ng --cpu 8 --io 4 --vm 2 --vm-bytes 128M --fork 4 --timeout 10s
root@awen-UBuntu:~# docker run -it --rm --name haha lorel/docker-stress-ng --vm 2 --vm-bytes 256M
root@awen-UBuntu:~# docker stats
CONTAINER ID NAME CPU % MEM USAGE / LIMIT MEM % NET I/O BLOCK I/O PIDS
40327a2417f9 haha 197.37% 516.4MiB / 1.896GiB 26.60% 946B / 0B 360kB / 0B 5
root@awen-UBuntu:~# docker run -it --rm --name haha -m 265m --memory-swap 1024m lorel/docker-stress-ng --vm 2 --vm-bytes 256M
root@awen-UBuntu:~# ps -ef | grep nginx
root 9631 9602 0 Oct27 ? 00:00:00 nginx: master process nginx -g daemon off;
systemd+ 9768 9631 0 Oct27 ? 00:00:00 nginx: worker process
root@awen-UBuntu:~# cat /proc/9602/cpuset
/system.slice/containerd.service
root@awen-UBuntu:~# cat /sys/fs/cgroup/system.slice/docker-ffcaecc0957d18e6dab963c74737d489c012f9af929762a89cb38e2bdb636f98.scope/cpu.max
100000 100000
1个cpu是1000毫核
内存
root@awen-UBuntu:~# cat /sys/fs/cgroup/system.slice/docker-ffcaecc0957d18e6dab963c74737d489c012f9af929762a89cb38e2bdb636f98.scope/memory.max
536870912(单位是字节)
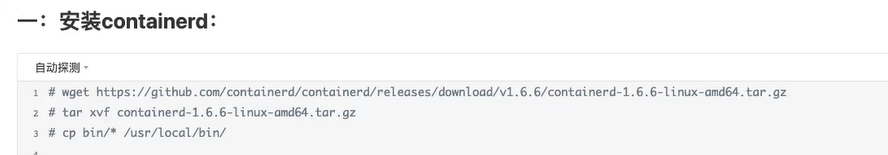
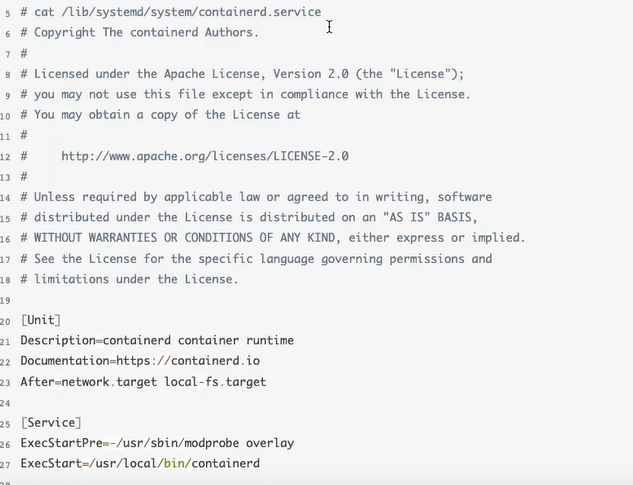
安装containerd
安装依赖包
root@awen-UBuntu:~# apt update
root@awen-UBuntu:~# apt install apt-transport-https ca-certificates curl software-properties-common
安装GPG证书
root@awen-UBuntu:~# curl -fsSL https://mirrors.aliyun.com/docker-ce/linux/ubuntu/gpg | sudo apt-key add -
写入软件信息原
root@awen-UBuntu:~# add-apt-repository "deb [arch=amd64] https://mirrors.aliyun.com/docker-ce/linux/ubuntu $(lsb_release -cs) stable"
root@awen-UBuntu:~# apt update
root@awen-UBuntu:~# apt-cache madison containerd.io
root@awen-UBuntu:~# apt install containerd.io
root@awen-UBuntu:~# ctr --version
ctr containerd.io 1.6.9
docker 是命令发给dockerd 再发给containerd,
打印containerd配置文件
root@awen-UBuntu:~# containerd config default
disabled_plugins = []
imports = []
oom_score = 0
plugin_dir = ""
required_plugins = []
root = "/var/lib/containerd"
state = "/run/containerd"
temp = ""
version = 2
[cgroup]
path = ""
[debug]
address = ""
format = ""
gid = 0
level = ""
uid = 0
[grpc]
address = "/run/containerd/containerd.sock"
gid = 0
max_recv_message_size = 16777216
max_send_message_size = 16777216
tcp_address = ""
tcp_tls_ca = ""
tcp_tls_cert = ""
tcp_tls_key = ""
uid = 0
[metrics]
address = ""
grpc_histogram = false
[plugins]
[plugins."io.containerd.gc.v1.scheduler"]
deletion_threshold = 0
mutation_threshold = 100
pause_threshold = 0.02
schedule_delay = "0s"
startup_delay = "100ms"
[plugins."io.containerd.grpc.v1.cri"]
device_ownership_from_security_context = false
disable_apparmor = false
disable_cgroup = false
disable_hugetlb_controller = true
disable_proc_mount = false
disable_tcp_service = true
enable_selinux = false
enable_tls_streaming = false
enable_unprivileged_icmp = false
enable_unprivileged_ports = false
ignore_image_defined_volumes = false
max_concurrent_downloads = 3
max_container_log_line_size = 16384
netns_mounts_under_state_dir = false
restrict_oom_score_adj = false
sandbox_image = "registry.k8s.io/pause:3.6"
selinux_category_range = 1024
stats_collect_period = 10
stream_idle_timeout = "4h0m0s"
stream_server_address = "127.0.0.1"
stream_server_port = "0"
systemd_cgroup = false
tolerate_missing_hugetlb_controller = true
unset_seccomp_profile = ""
[plugins."io.containerd.grpc.v1.cri".cni]
bin_dir = "/opt/cni/bin"
conf_dir = "/etc/cni/net.d"
conf_template = ""
ip_pref = ""
max_conf_num = 1
[plugins."io.containerd.grpc.v1.cri".containerd]
default_runtime_name = "runc"
disable_snapshot_annotations = true
discard_unpacked_layers = false
ignore_rdt_not_enabled_errors = false
no_pivot = false
snapshotter = "overlayfs"
[plugins."io.containerd.grpc.v1.cri".containerd.default_runtime]
base_runtime_spec = ""
cni_conf_dir = ""
cni_max_conf_num = 0
container_annotations = []
pod_annotations = []
privileged_without_host_devices = false
runtime_engine = ""
runtime_path = ""
runtime_root = ""
runtime_type = ""
[plugins."io.containerd.grpc.v1.cri".containerd.default_runtime.options]
[plugins."io.containerd.grpc.v1.cri".containerd.runtimes]
[plugins."io.containerd.grpc.v1.cri".containerd.runtimes.runc]
base_runtime_spec = ""
cni_conf_dir = ""
cni_max_conf_num = 0
container_annotations = []
pod_annotations = []
privileged_without_host_devices = false
runtime_engine = ""
runtime_path = ""
runtime_root = ""
runtime_type = "io.containerd.runc.v2"
[plugins."io.containerd.grpc.v1.cri".containerd.runtimes.runc.options]
BinaryName = ""
CriuImagePath = ""
CriuPath = ""
CriuWorkPath = ""
IoGid = 0
IoUid = 0
NoNewKeyring = false
NoPivotRoot = false
Root = ""
ShimCgroup = ""
SystemdCgroup = false
[plugins."io.containerd.grpc.v1.cri".containerd.untrusted_workload_runtime]
base_runtime_spec = ""
cni_conf_dir = ""
cni_max_conf_num = 0
container_annotations = []
pod_annotations = []
privileged_without_host_devices = false
runtime_engine = ""
runtime_path = ""
runtime_root = ""
runtime_type = ""
[plugins."io.containerd.grpc.v1.cri".containerd.untrusted_workload_runtime.options]
[plugins."io.containerd.grpc.v1.cri".image_decryption]
key_model = "node"
[plugins."io.containerd.grpc.v1.cri".registry]
config_path = ""
[plugins."io.containerd.grpc.v1.cri".registry.auths]
[plugins."io.containerd.grpc.v1.cri".registry.configs]
[plugins."io.containerd.grpc.v1.cri".registry.headers]
[plugins."io.containerd.grpc.v1.cri".registry.mirrors]
[plugins."io.containerd.grpc.v1.cri".x509_key_pair_streaming]
tls_cert_file = ""
tls_key_file = ""
[plugins."io.containerd.internal.v1.opt"]
path = "/opt/containerd"
[plugins."io.containerd.internal.v1.restart"]
interval = "10s"
[plugins."io.containerd.internal.v1.tracing"]
sampling_ratio = 1.0
service_name = "containerd"
[plugins."io.containerd.metadata.v1.bolt"]
content_sharing_policy = "shared"
[plugins."io.containerd.monitor.v1.cgroups"]
no_prometheus = false
[plugins."io.containerd.runtime.v1.linux"]
no_shim = false
runtime = "runc"
runtime_root = ""
shim = "containerd-shim"
shim_debug = false
[plugins."io.containerd.runtime.v2.task"]
platforms = ["linux/amd64"]
sched_core = false
[plugins."io.containerd.service.v1.diff-service"]
default = ["walking"]
[plugins."io.containerd.service.v1.tasks-service"]
rdt_config_file = ""
[plugins."io.containerd.snapshotter.v1.aufs"]
root_path = ""
[plugins."io.containerd.snapshotter.v1.btrfs"]
root_path = ""
[plugins."io.containerd.snapshotter.v1.devmapper"]
async_remove = false
base_image_size = ""
discard_blocks = false
fs_options = ""
fs_type = ""
pool_name = ""
root_path = ""
[plugins."io.containerd.snapshotter.v1.native"]
root_path = ""
[plugins."io.containerd.snapshotter.v1.overlayfs"]
root_path = ""
upperdir_label = false
[plugins."io.containerd.snapshotter.v1.zfs"]
root_path = ""
[plugins."io.containerd.tracing.processor.v1.otlp"]
endpoint = ""
insecure = false
protocol = ""
[proxy_plugins]
[stream_processors]
[stream_processors."io.containerd.ocicrypt.decoder.v1.tar"]
accepts = ["application/vnd.oci.image.layer.v1.tar+encrypted"]
args = ["--decryption-keys-path", "/etc/containerd/ocicrypt/keys"]
env = ["OCICRYPT_KEYPROVIDER_CONFIG=/etc/containerd/ocicrypt/ocicrypt_keyprovider.conf"]
path = "ctd-decoder"
returns = "application/vnd.oci.image.layer.v1.tar"
[stream_processors."io.containerd.ocicrypt.decoder.v1.tar.gzip"]
accepts = ["application/vnd.oci.image.layer.v1.tar+gzip+encrypted"]
args = ["--decryption-keys-path", "/etc/containerd/ocicrypt/keys"]
env = ["OCICRYPT_KEYPROVIDER_CONFIG=/etc/containerd/ocicrypt/ocicrypt_keyprovider.conf"]
path = "ctd-decoder"
returns = "application/vnd.oci.image.layer.v1.tar+gzip"
[timeouts]
"io.containerd.timeout.bolt.open" = "0s"
"io.containerd.timeout.shim.cleanup" = "5s"
"io.containerd.timeout.shim.load" = "5s"
"io.containerd.timeout.shim.shutdown" = "3s"
"io.containerd.timeout.task.state" = "2s"
[ttrpc]
address = ""
gid = 0
uid = 0
覆盖配置文件
root@awen-UBuntu:~# containerd config default > /etc/containerd/config.toml
修改配置文件
61 sandbox_image = "registry.k8s.io/pause:3.6"
sandbox_image = "registry.aliyuncs.com/google_containers/pause:3.7"
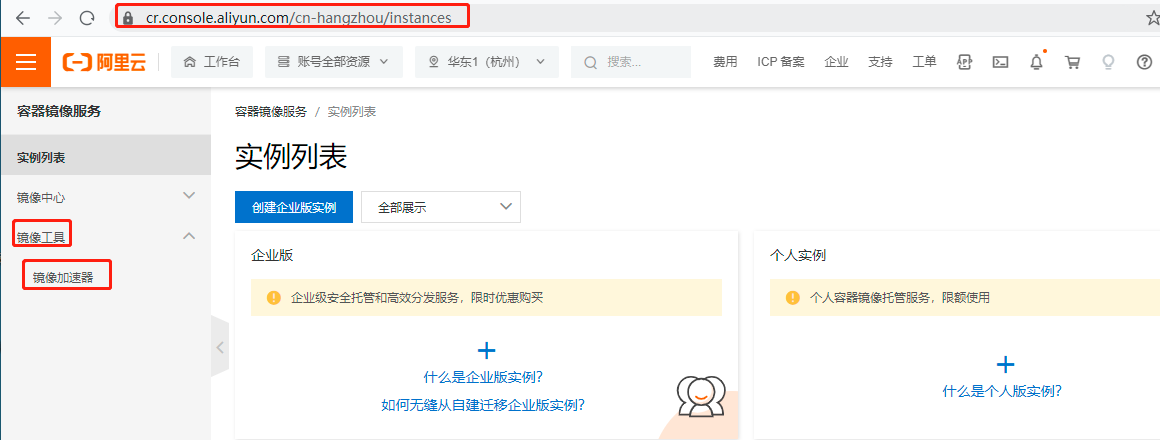
配置镜像加速
cr
153 [plugins."io.containerd.grpc.v1.cri".registry.mirrors]
154 [plugins."io.containerd.grpc.v1.cri".registry.mirrors."docker.io"]
155 endpoint = ["https://9916w1ow.mirror.aliyuncs.com"]
加速地址
https://ydwu9nbq.mirror.aliyuncs.com
https://cr.console.aliyun.com/

重启container
root@awen-UBuntu:~# systemctl restart containerd.service
安装runc
root@awen-UBuntu:~# wget https://github.com/opencontainers/runc/releases/download/v1.1.4/runc.amd64
root@awen-UBuntu:~# runc -v
runc version 1.1.4
commit: v1.1.4-0-g5fd4c4d
spec: 1.0.2-dev
go: go1.18.7
libseccomp: 2.5.1
网络自己配
安装cni
root@awen-UBuntu:~# nerdctl exec -it bd311525042a sh
/ # ls
containerd可以使用docker镜像
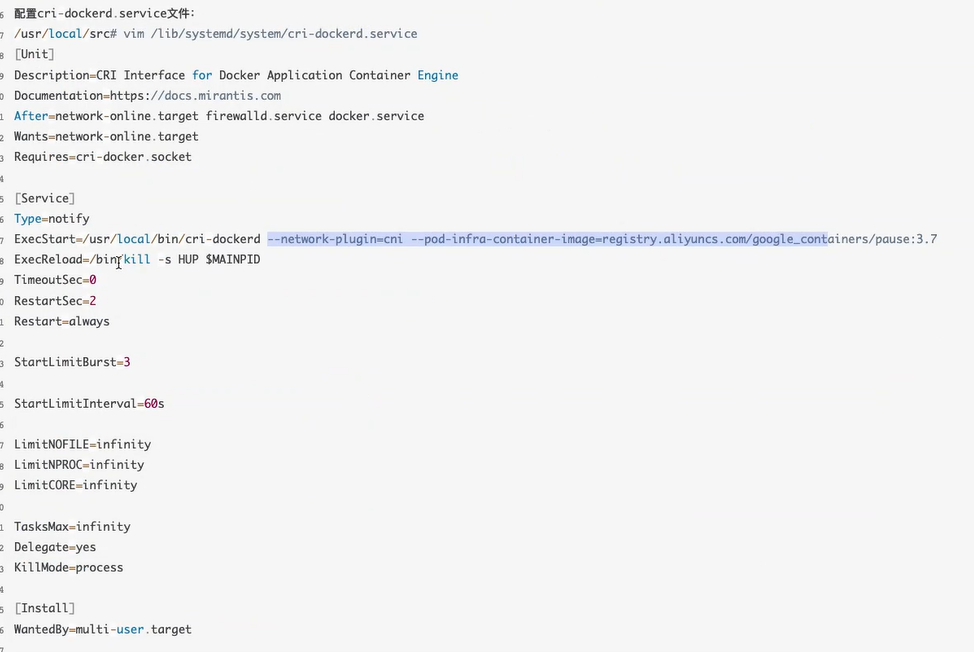
1.24版本的k8s 使用docker 安装cri-docker.service
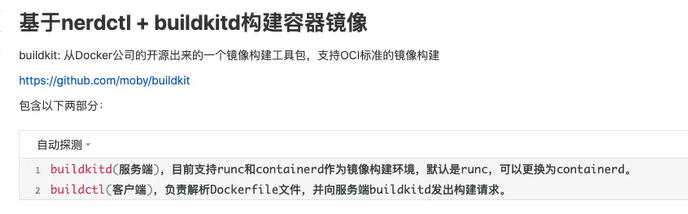
containerd构建镜像
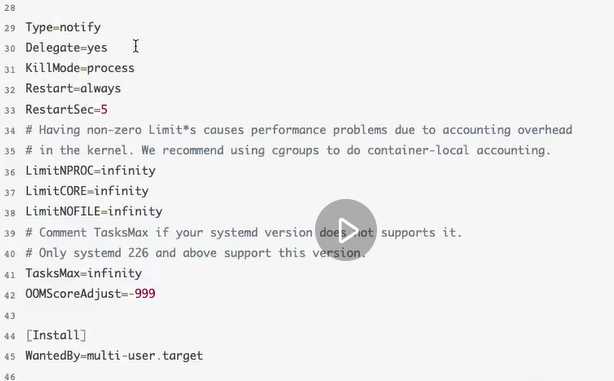
安装harbor
下载地址
https://github.com/goharbor/harbor/releases/
root@awen-UBuntu:~# wget https://github.com/goharbor/harbor/releases/download/v2.6.1/harbor-offline-installer-v2.6.1.tgz
root@awen-UBuntu:~# tar xf harbor-offline-installer-v2.6.1.tgz -C /apps
root@awen-UBuntu:~# tar xf harbor-offline-installer-v2.6.1.tgz -C /apps
root@awen-UBuntu:~# cd /apps
root@awen-UBuntu:/apps# ls
harbor
root@awen-UBuntu:/apps# cd harbor/
root@awen-UBuntu:/apps/harbor# ls
common.sh harbor.v2.6.1.tar.gz harbor.yml.tmpl install.sh LICENSE prepare
root@awen-UBuntu:/apps/harbor# cp harbor.yml.tmpl harbor.yml
root@awen-UBuntu:/apps/harbor# vi harbor.yml
hostname: ip/域名
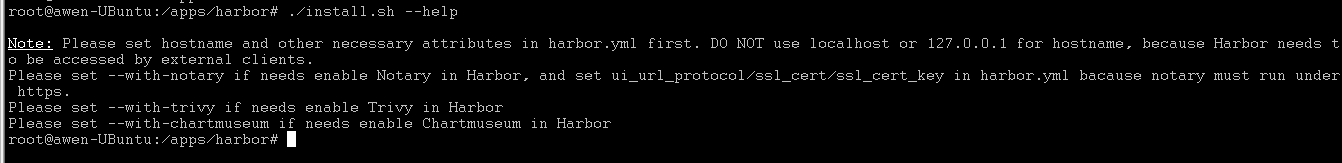
--with-notary 做可行性验证 需要ssl
--with-trivy 对镜像进行漏洞扫描的组件
--with-chartmuseum helm 中chart格式的镜像
root@awen-UBuntu:/apps/harbor# ./install.sh --with-trivy --with-chartmuseum
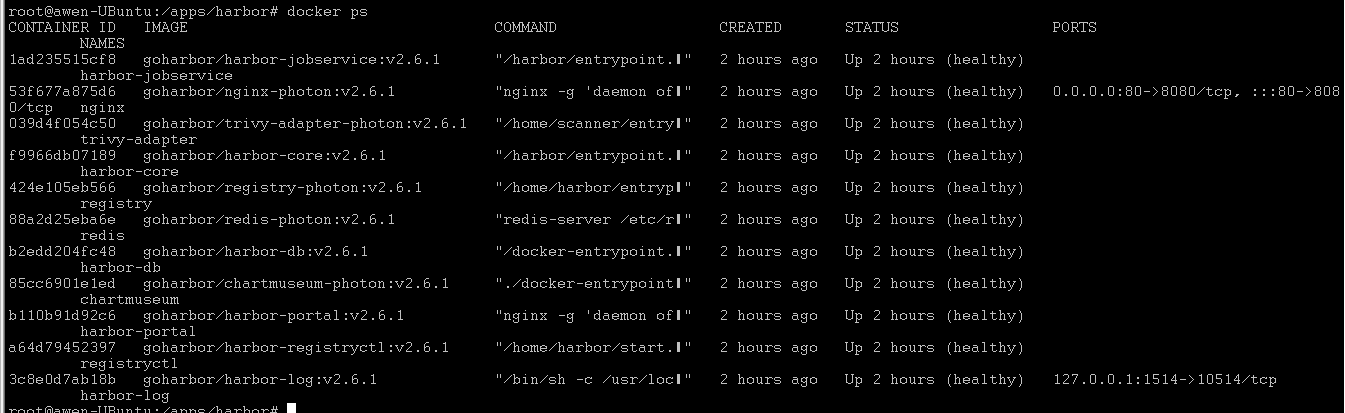
登录harbor仓库
root@awen-UBuntu:~# docker login 10.4.7.128
Username: admin
Password:
WARNING! Your password will be stored unencrypted in /root/.docker/config.json.
Configure a credential helper to remove this warning. See
https://docs.docker.com/engine/reference/commandline/login/#credentials-store
Login Succeeded
密码文件
root@awen-UBuntu:~# cat /root/.docker/config.json
解密harbor密码
root@awen-UBuntu:~# echo xxxxxxxxxxx| base64 -d
上传镜像脚本
root@awen-UBuntu:~# cat build-command.sh
#!/bin/bash
TAG=$1
docker build -t harbor.xxx.cn/awen/server-web1:${TAG} .
docker push harbor.xxx.cn/awen/server-web1:${TAG}

最新文章
- java web学习总结(三十一) -------------------EL表达式
- poj2407
- Hive(四):c#通过odbc访问hive
- 发现木马C:\windows\system32\FastUserSwitchingCompatibilityex.dll
- EF异常:WebForm、Console、Winform层不引入EF报错
- Windows下memcache安装使用
- if...else..的错误用法
- 愉快的开始 - 零基础入门学习Python000
- epoll相关
- Natas Wargame Level 13 Writeup(文件上传漏洞,篡改file signature,Exif)
- linux下SS 网络命令详解
- linux Ubuntu系统安装百度aip
- [P1329] 数列
- 【转】Windows下charles 使用教程指南
- WeakHashMap<K,V> 中的弱引用
- redis学习历程
- 基于OVS的VLAN虚拟化简易实践方案
- Linux shell while
- PAT乙级1027
- Percona 工具 pt-query-digest的使用